Network Address Translation is one of the most fundamental technologies in networking. It allows us to modify IP addresses as packets pass through a router.
1) Static NAT
One-to-one mapping between a private and public IP. Used for: devices that must always be reachable.
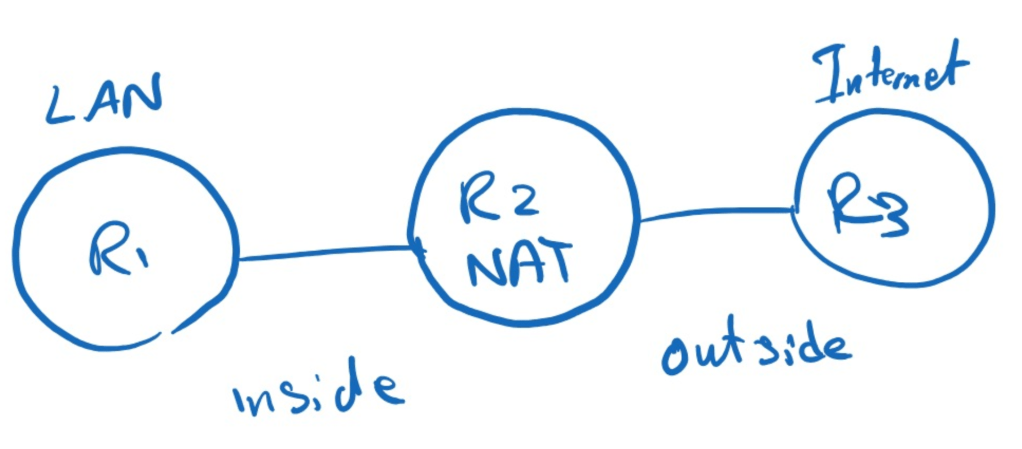
Config (on R2):
interface f0/0
ip nat inside
interface f1/0
ip nat outside
ip nat inside source static 192.168.1.10 200.1.1.10
192.168.1.10 is always translated to 200.1.1.10 (Fixed mapping).
2) Dynamic NAT
Translate inside hosts using a pool of public IPs.
Config:
ip nat pool MYPOOL 200.1.1.10 200.1.1.20 netmask 255.255.255.0
access-list 1 permit 192.168.1.0 0.0.0.255
ip nat inside source list 1 pool MYPOOL
Each inside host gets a unique public IP from the pool (Limited by pool size).
3) PAT (NAT Overload)
Here many hosts share one public IP.
Config:
Uses port numbers to differentiate sessions (Many-to-one translation).
4) Port Forwarding (Static PAT)
Expose internal services (e.g. web server)
Config:
ip nat inside source static tcp 192.168.1.10 80 200.1.1.10 80
External users connect to 200.1.1.10:80 –> Traffic is forwarded to 192.168.1.10:80
5) NAT Extendable
Allow overlapping static NAT entries. (Allows multiple mappings with same IP but different contexts)
Config:
ip nat inside source static 192.168.1.10 200.1.1.10 extendable
ip nat inside source static 192.168.1.10 200.1.1.20 extendable
6) NAT with Route-Map
Selective NAT based on: destination, interface or policy.
Config:
access-list 101 permit ip 192.168.1.0 0.0.0.255 any
route-map NAT permit 10
match ip address 101
ip nat inside source route-map NAT interface f1/0 overload
It can also match the interface of exit:
route-map NAT1 permit 10
match interface X
route-map NAT2 permit 10
match interface Y
ip nat inside source route-map NAT1 interface f1/0 overload
ip nat inside source route-map NAT2 interface f2/0 overload
We can have multiple NAT statement the order of them are very important, so if the traffic is matched with one of them it will not be checked by the next NAT statement.
So if in this situation we should deny the source in upper NAT statement in order to prevent the match.
7) NAT TCP Load Balancing
Distribute traffic across multiple servers.
Config:
ip nat pool WEBPOOL 192.168.1.10 192.168.1.12 netmask 255.255.255.0
ip nat inside destination list 1 pool WEBPOOL
access-list 1 permit tcp any host 200.1.1.10 eq 80
ip alias 200.1.1.10
#This creates a fake IP on the NAT router
8) NAT Virtual Interface (NVI)
NAT without inside/outside interfaces.
Config:
ip nat pool MYPOOL 192.168.23.100 192.168.23.200 prefix-length 24 add-route
ip nat source list 1 pool MYPOOL
access-list 1 permit 192.168.12.0 0.0.0.255
#add-route >It tells the router to automatically install a route for the NAT pool. That way, return traffic for translated addresses knows how to come back correctly.
Leave a comment